Difference between revisions of "Access control"
From AMTech WikiDocs
(→Actors) |
(→Policies) |
||
| Line 40: | Line 40: | ||
**Delete (delete resources of this type) | **Delete (delete resources of this type) | ||
;if Check user is flag the polices will enforce that the user must own the resource to CRUD it | ;if Check user is flag the polices will enforce that the user must own the resource to CRUD it | ||
| − | [[File:Actor-polices.png| | + | [[File:Actor-polices.png|880px|thumbnail|center|Actor policies]] |
== Tenants == | == Tenants == | ||
Revision as of 15:14, 25 May 2016
Access control is applied based on the info of the resource being accessed, validating it against the info of the user accessing the resource. The verifications for access control are :
- access to the resource type (using user roles/actors)
- access to the resource tenant and guest tenants (using the user's tenant)
- access to the resources owner (using the user accessing the resource)
This validations are performed in order.
Contents
How it works
Multitenancy
Amtech IoT platform is multitenant , with the goals of :
- Protecting resources that belong to a tenant
- Sharing resources among tenants based on the guesttenants/guestusers properties of the resources
Roles
Roles are resources that define the access control policies for the core resources.
- They specify the HTTP operations allowed on a given resource type.
- They are associated to users
- They are system managed.
- There are 2 main roles : activityCreator and follower. A user can only be one of both
- Users with the roles activityCreator will have access to thing types and observation types
- the admin tenant can remove or add members using the options team and invite respectively
- PaaS functionality
- Users with the roles follower will have the access their actors define (See Actors)
- the admin tenant can remove or add members using the options team and invite respectively
- SaaS configuration functionality
Actors
Actors are resources that defined access to specific thing types and notification types
- They specify the HTTP operations allowed the the type
- They are associated to users with the role follower via the subscription to a service or the invitation of new users
- Actors can include a restriction to apply the access control using the target resource user (meaning that the access control will be applied verifying access to type, tenant and user)
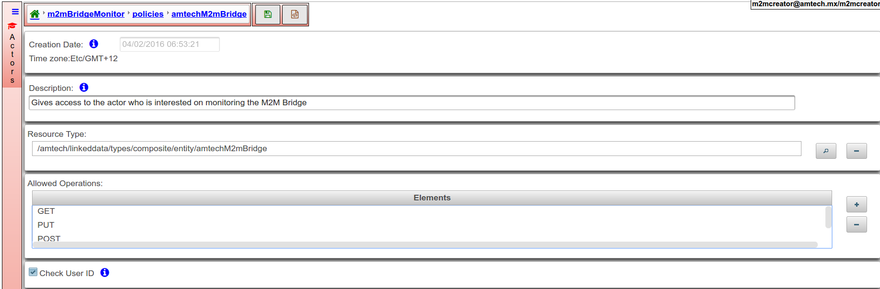
Policies
A police encompasses
- A Thing type
- The set of CRUD operations that can be execute over selected Thing type
- Create (create a new resource of the type)
- Read (read resources of this type)
- Update (update resources of this type)
- Delete (delete resources of this type)
- if Check user is flag the polices will enforce that the user must own the resource to CRUD it
Tenants
- All resources have the tenant that owns it (the tenant of the user that created the resource), and may also define the list of guest tenants, that will have read access to the resource.
- The tenant of a resource is automatically assigned when the resource is created and cannot be modified.
- The list of guest tenants of a resource can be assigned by the user.
Users
- The user id must be an email (to be redefined in future versions)
- A user can belong to multiple tenants, it may have multiple actors, but it only have one role (activityCreator or follower)
- Users are related to the resources regarding access control:
- All resources have the user that owns it (the user that created the resource), and may also define the list of guest users, that will have access to the resource according to their actors
- The user of a resource is automatically assigned when the resource is created and cannot be modified.
- The list of guest users of a resource can be assigned anytime
Access control properties in resources
- Things and observations types have 4 properties to govern access control
- _tenant assigned by the DAP, value is set to the tenant that creates the resource
- _user assigned by the DAP, value is set to the user that creates the resource
- guesttenants can be assigned by the user that created the resource
- guestusers can be assigned by the user that created the resource